Smoothwall, a web filtering system, can be bypassed using techniques like proxy servers, VPNs, and DNS manipulation. However, bypassing may have legal consequences, so users must proceed cautiously, ensuring compliance with regulations and obtaining proper authorization.
What is Smoothwall?
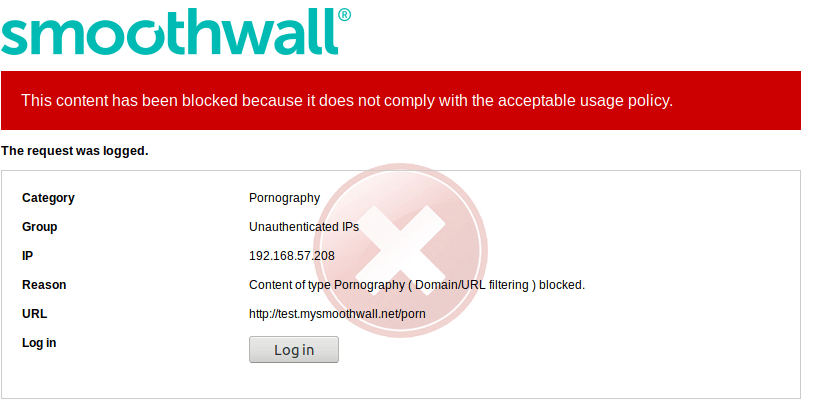
Smoothwall is a web filtering software that restricts access to certain websites and content based on predefined rules and categories. It is often used by schools and businesses to control internet access and ensure a safe browsing experience for users.
How Smoothwall Works
Smoothwall works based on cutting-edge technology to filter and monitor internet traffic, ensuring a safe and secure online experience for users. Here is how Smoothwall works:
- Content filtering: Smoothwall uses advanced algorithms to block access to inappropriate or harmful websites.
- Anomaly detection: It identifies abnormal behavior and alerts administrators to potential security threats.
- Reporting and analytics: This app provides detailed reports on internet usage, allowing administrators to track trends and patterns.
- Real-time monitoring: Smoothwall continuously scans network traffic to detect and prevent malicious activity.
The Legality of Bypassing Smoothwall
Bypassing Smoothwall, a web filter system used in schools and organizations, may raise questions about legality. Users often attempt to bypass the system in order to access restricted websites or content. While bypassing Smoothwall may seem harmless to some, it is important to consider the legal implications involved.
In most cases, bypassing Smoothwall is a violation of acceptable use policies set by schools or organizations. Punishments for bypassing may include disciplinary action or legal consequences. It is crucial for users to understand the risks associated with attempting to bypass web filters like Smoothwall.
Preparing to Bypass Smoothwall
Before attempting to bypass Smoothwall filters, users should take certain precautions to mitigate risks and ensure successful execution. This may include:
- Understanding the network topology and security architecture.
- Identifying potential entry points or vulnerabilities in the system.
- Gether necessary tools and resources for bypassing techniques.
- Get appropriate permissions or authorization from relevant authorities.
Common Smoothwall Bypass Techniques
- Proxy Servers: Proxy servers act as intermediaries between users and the internet. By routing internet traffic through a proxy server located outside the network, users can access blocked websites indirectly. This method disguises the origin of the traffic, making it difficult for Smoothwall to detect and block.
- Virtual Private Networks (VPNs): VPNs establish encrypted connections to remote servers, effectively masking the user’s IP address and location. By tunneling traffic through the VPN server, users can bypass Smoothwall filtering and access restricted content securely. VPNs are particularly effective in circumventing geo-restrictions and censorship.
- DNS Manipulation: DNS manipulation involves altering DNS settings to bypass domain-based filtering implemented by Smoothwall. Users can change their DNS servers to those that are not subject to filtering or utilize DNS tunneling techniques to evade detection. This method allows access to blocked websites by resolving their domain names to alternative IP addresses.
- URL Shorteners: URL shortening services can be used to obfuscate blocked URLs, making them appear as innocuous links. By converting the original URL into a shortened form, users can evade detection by Smoothwall’s URL filtering mechanisms. However, this method may not always be reliable and can be circumvented by more advanced filtering techniques.
- Encrypted Connections: Utilizing HTTPS or SSL/TLS encryption can help bypass content inspection performed by Smoothwall. By encrypting the communication between the user’s device and the web server, sensitive data, including the requested URL, remains hidden from prying eyes. This makes it challenging for Smoothwall to analyze and block the traffic based on its content.
Advanced Smoothwall Bypass Strategies
Advanced Smoothwall bypass strategies include sophisticated methods to circumvent filtering and access restricted content. These techniques require a deeper understanding of network protocols and security mechanisms. Below are some advanced strategies:
- Tunneling Protocols: You can use protocols like SSH tunneling or VPN over SSH to bypass filtering. By encapsulating network traffic within secure tunnels, these protocols conceal the nature of the transmitted data, making it difficult for Smoothwall to inspect and block.
- Protocol Obfuscation: Another effective strategy is to Modify network traffic to disguise bypass attempts. Techniques such as packet fragmentation, altering packet headers, or encoding data payloads can obscure the true nature of the communication, making it challenging for Smoothwall to detect and block.
- Packet Fragmentation: You can break data packets into smaller fragments to evade detection. By fragmenting packets into smaller sizes, bypassing traffic can bypass deep packet inspection mechanisms employed by Smoothwall, reducing the likelihood of detection and blocking.
- Domain Fronting: You can use content delivery networks (CDNs) to disguise traffic origins. By routing traffic through popular CDN providers, bypassing attempts can appear as legitimate CDN traffic, making it challenging for Smoothwall to differentiate between authorized and unauthorized connections.
Tips for Successful Smoothwall Bypassing
To increase the chance of successful bypassing, users should consider the following tips:
- Regularly update bypassing tools and techniques to adapt to changing security measures.
- You should be cautious and discreet when bypassing filters to prevent detection or legal trouble.
- Test bypassing methods in controlled environments before applying them in production networks.
- Respect network policies and avoid engaging in activities that may compromise security or integrity.
- Stay informed about new developments in web filtering technology and countermeasures.
Final Thoughts
In conclusion, bypassing Smoothwall and other web filters can be a useful skill to have in certain situations. By understanding how Smoothwall works, preparing properly, and using the right techniques and strategies, you can successfully bypass the filter when needed. Just remember to do so responsibly and ethically to avoid any potential consequences.
References:
https://kb.smoothwall.com/hc/en-us/articles/360003223940-Bypassing-the-Smoothwall-Filter
https://security.meta.stackexchange.com/questions/1488/blocked-by-smoothwall
Hello, I’m Herman C. Miller, the founder of InternetPKG.com, your ultimate destination for all things Mobile Internet and Telecommunication Services. With a BSc in Telecommunication Services and over 6 years at AT&T, my passion for the industry led to this platform. At InternetPKG.com, we prioritize keeping you informed with the latest package offers, ensuring our content stays current. Our team, including a dedicated Internet Package and Mobile Data Plans Researcher, tirelessly researches emerging trends, identifies market opportunities, and provides expert product recommendations.
